Thin core
The core owns routing, context, session, tooling, and execution orchestration. It does not absorb each platform's business rules.
Personal agents such as OpenClaw are optimized for individual tools and user-owned setup. AtlasClaw separates core orchestration from provider contracts so multi-user deployment, governed execution, and enterprise system boundaries can hold in production.
AtlasClaw stays useful by keeping boundaries stable instead of swallowing every integration concern into the core.
The core owns routing, context, session, tooling, and execution orchestration. It does not absorb each platform's business rules.
Each provider packages auth behavior, skills, scripts, references, and normalization for a target system.
AtlasClaw passes through real user identity boundaries and lets target platforms keep authorization and auditing where they already belong.
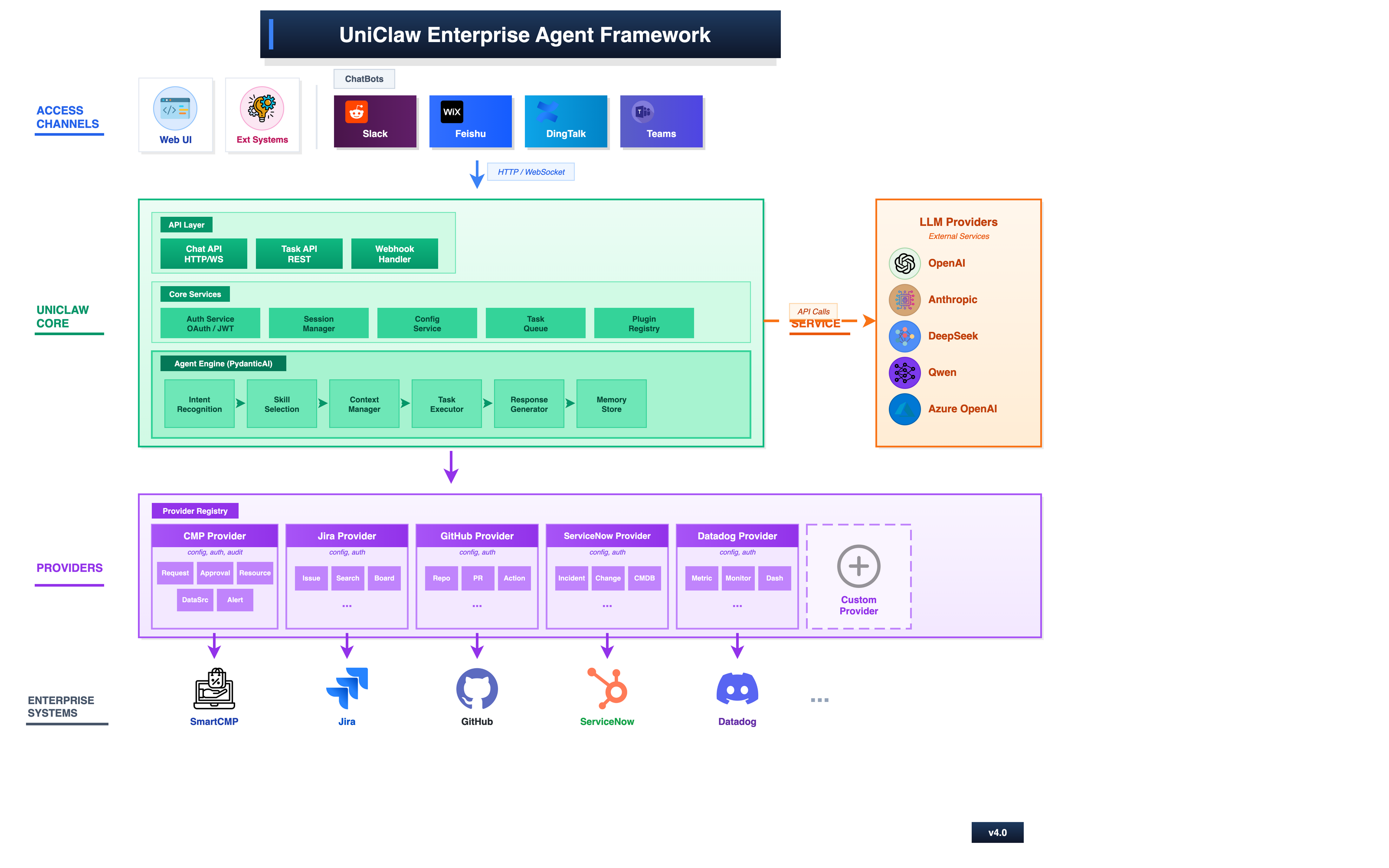
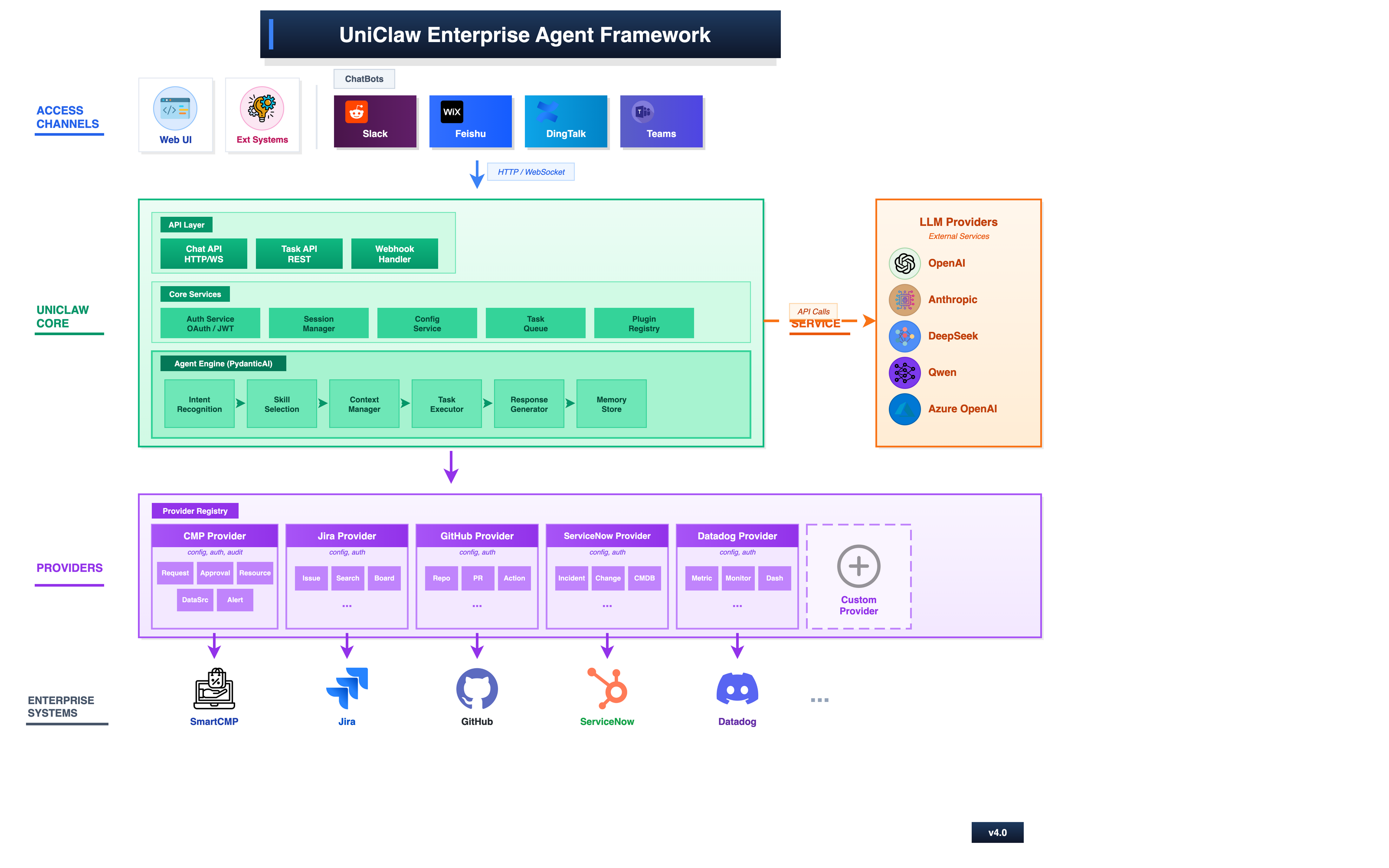 Click to enlarge
Click to enlarge From channel entrypoints to the core, then outward through providers to enterprise systems, the execution path remains explicit.
From channel entrypoints to the core, then outward through providers to enterprise systems, the execution path remains explicit.
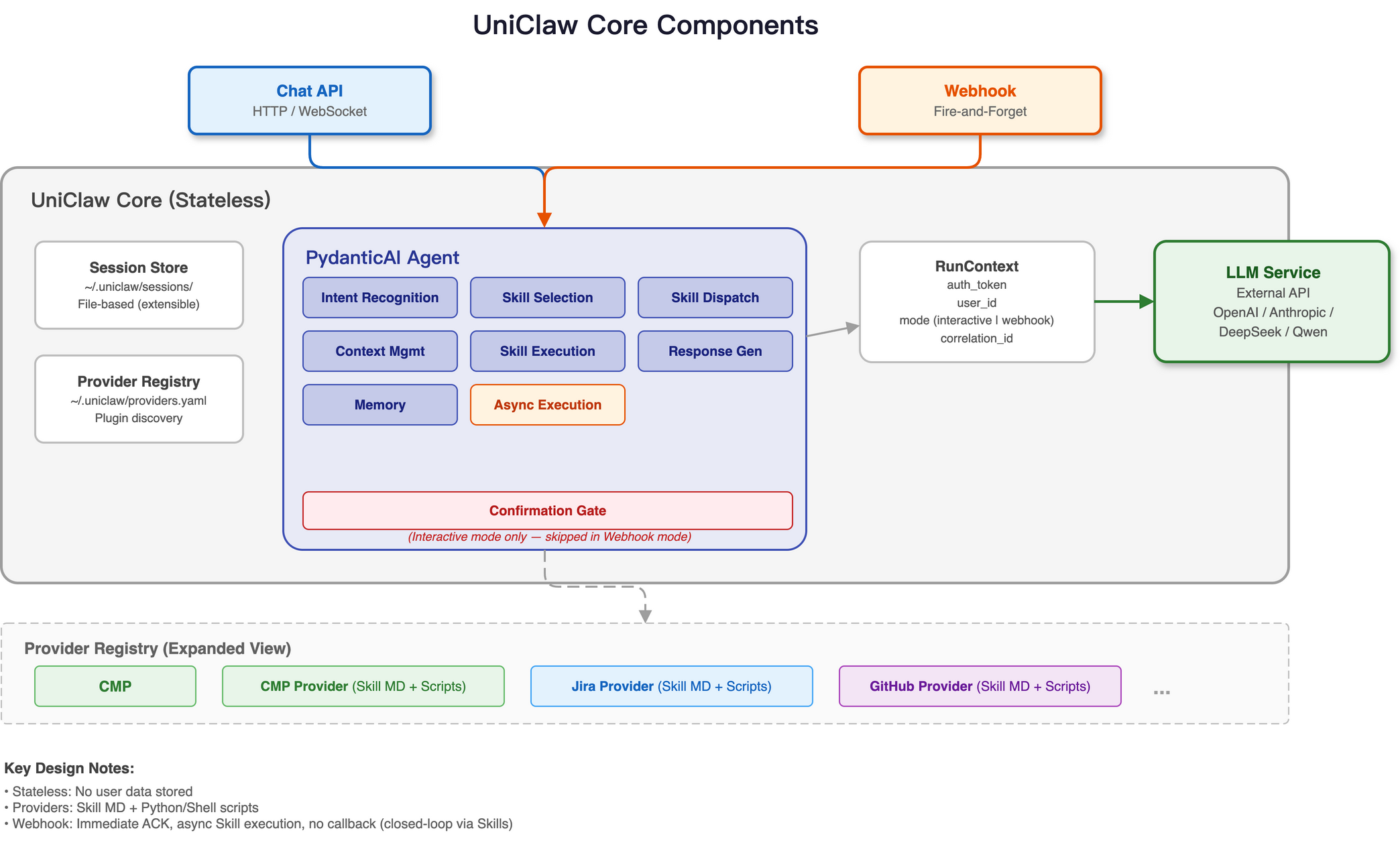
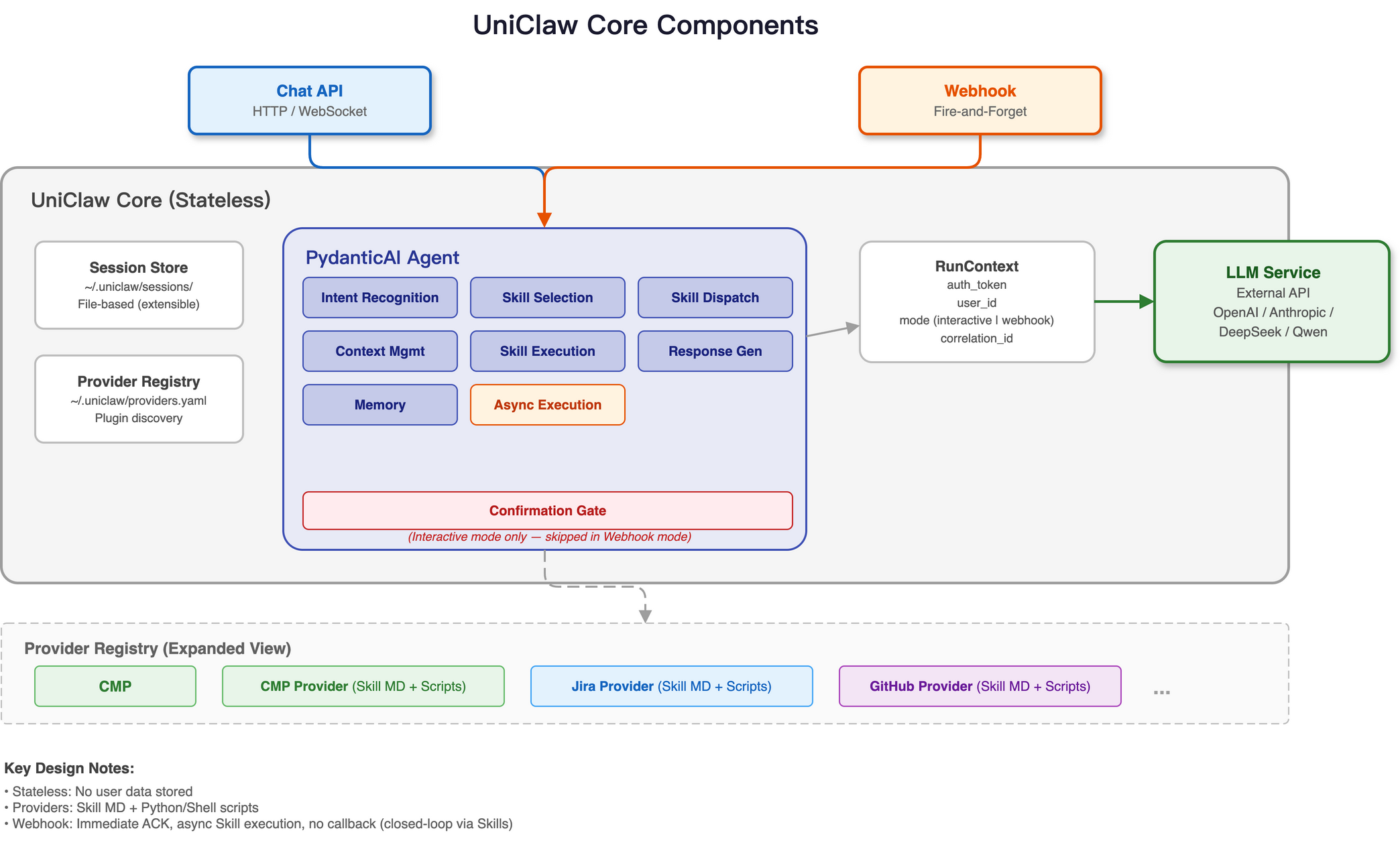 Click to enlarge
Click to enlarge API services, session context, the agent engine, tools, and the provider registry form the reusable substrate.
API services, session context, the agent engine, tools, and the provider registry form the reusable substrate.
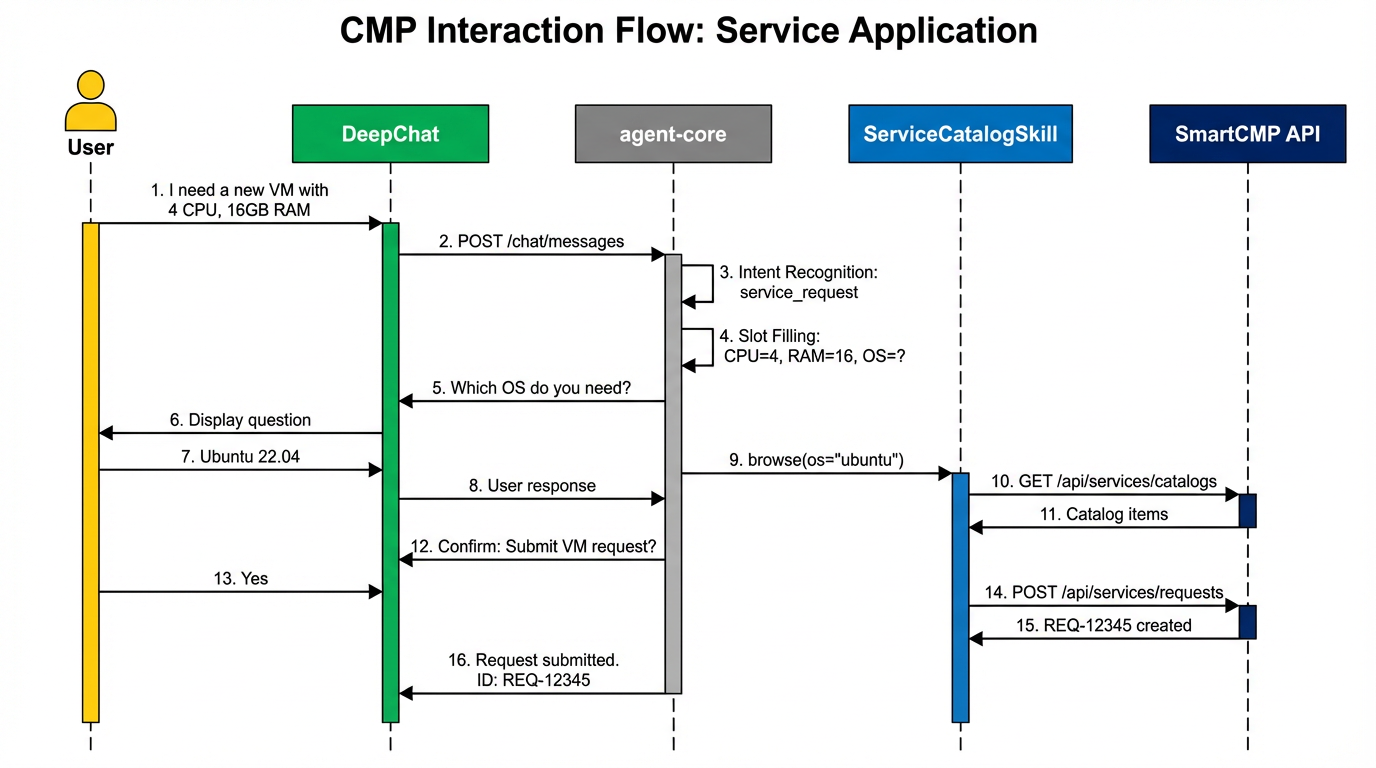
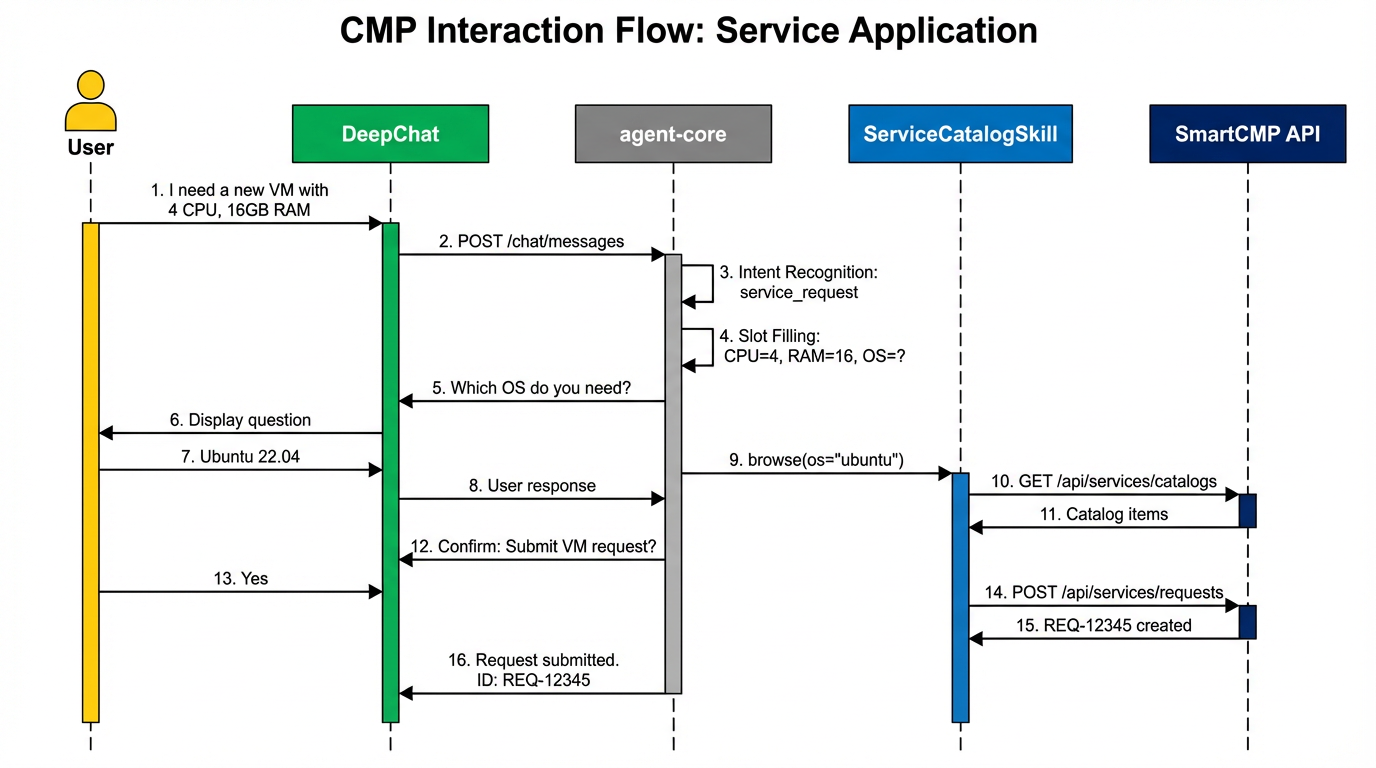 Click to enlarge
Click to enlarge The SmartCMP flow shows how requests, approvals, and platform execution can be organized inside a provider model.
The SmartCMP flow shows how requests, approvals, and platform execution can be organized inside a provider model.
Personal agents such as OpenClaw fit individual productivity well. Enterprise environments need shared deployment, governed access, provider contracts, and system-side audit boundaries, which AtlasClaw makes explicit.
Provider-qualified naming prevents collisions, keeps execution explicit, and makes webhook dispatch safer.
Some teams need an in-product AI module. Others need a multi-user cross-system agent layer. AtlasClaw supports both without changing the core mental model.
Webhook entrypoints and provider-qualified skills let existing systems call AtlasClaw as an AI execution layer, so traditional products can gain LLM capability without rebuilding their own agent stack.
Once the architecture is clear, the next step is understanding how AtlasClaw organizes external systems as providers.